The Game Developers Conference brings the game development community together. This year there will be thousands of attendees in San Francisco, CA the week of March 21st.
The CleanSpeak team will be among them, and we’d love to see you.
Continue reading →
These content moderation trends include relevant topics to content moderation in 2022 for social networks and other businesses.
Continue reading →
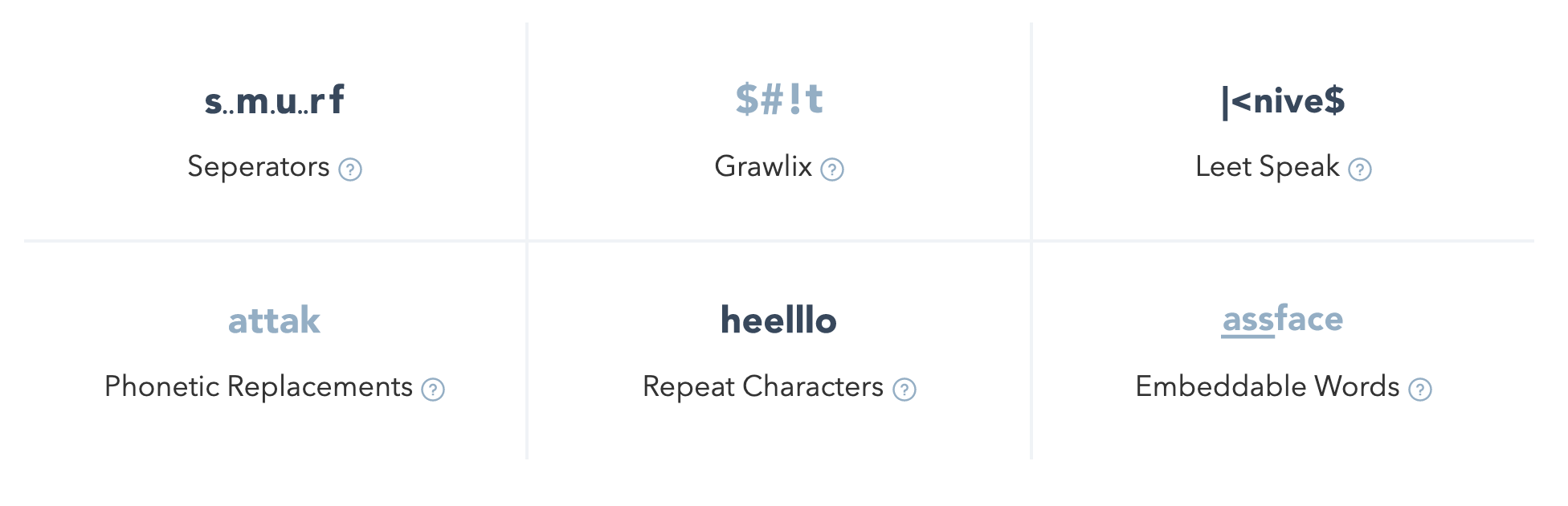
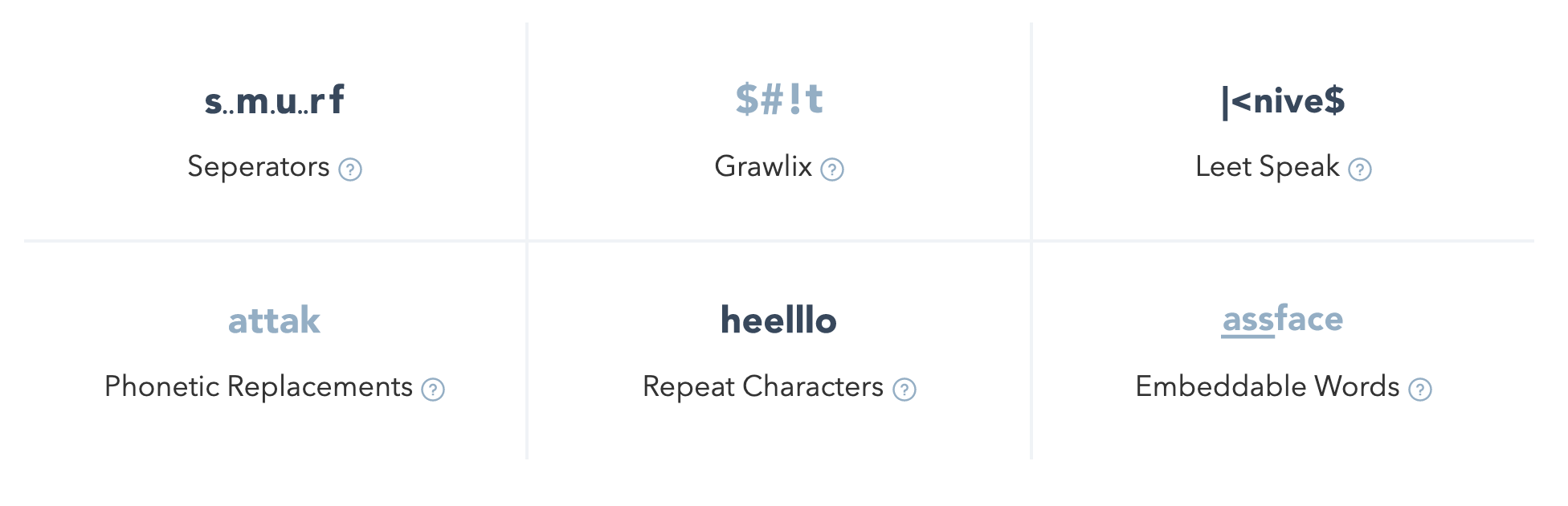
These profanity filtering and content moderation best practices include key platform requirements and essential tools for enterprise-scale advanced filtering systems.
Continue reading →

You may have heard of user-generated content (UGC) before, but what does it actually mean? UGC refers to any type of media produced by users rather than the company that owns or operates the platform where the media gets shared. Examples include YouTube or Facebook. Content such as photos, videos, comments, and product reviews are all examples of UGC.
Continue reading →

The recent announcement of CVE-2021-44228, which allows for "arbitrary code loaded from LDAP servers when message lookup substitution is enabled" through a vulnerability in Log4j has many people double checking the dependencies of their Java applications.
CleanSpeak is not affected
CleanSpeak is not affected by this vulnerability in Log4j. CleanSpeak uses a different logging framework, Logback, so there is no way that any CleanSpeak applications could be compromised.
Continue reading →